SUGCON Europe 2026: Harvest Now, Decrypt Later: A Sitecore Security Wake-Up Call
Akshay Sura - Partner
16 Apr 2026
Notes from Harald Greve's SUGCON Europe 2026 talk, and why every Sitecore team handling sensitive data should be paying attention.
The talk that stopped me in my tracks
At SUGCON Europe 2026 in London, Harald Greve (Engineering Manager at Macmillan Cancer Support and a 2026 Sitecore Technology MVP) gave one of those sessions that you leave thinking about on the ride home. The topic was quantum computing and what it means for the way we encrypt web traffic today. Read his LinkedIn article on post-quantum cryptography and then come back here.
Harald framed the problem the way only someone who works at a cancer charity can. The data his team protects is special category data under GDPR. It belongs to people who gave it up at one of the hardest moments of their lives. A breach isn't just a compliance headline. It's a betrayal.
That framing lands harder at a cancer charity, but the underlying point applies to anyone running a Sitecore site that collects sensitive information. Forms, logins, customer records, payment details, anything you'd rather not see on the front page of a newspaper in 2035.
The history lesson is the point
Harald opened with Bletchley Park. He and his wife had visited recently, and he drew a straight line from the Enigma codebreakers in the 1940s to where we are now. The British and allies broke ciphers that the Germans thought were unbreakable. The messages they decoded helped win the war.
Eighty-five years later, we're facing the same shape of problem. A more powerful machine is coming. Can we protect our communications before it arrives?
The answer has to be proactive, not reactive. Once the data is out, it's out.
Quantum, briefly
A traditional bit is a zero or a one. A qubit can be a zero, a one, or both at once. Three traditional bits hold one of eight states. Three qubits hold a superposition of all eight states at the same time. That parallelism is what lets a quantum computer chew through problems that would take a classical machine longer than the age of the universe.
Microsoft is targeting quantum capabilities in Azure by 2029 and in Microsoft 365 by 2033. Nation states are pouring money into it. Some of that work is being subcontracted to organized criminal groups, and some of those groups are already busy collecting data today.
Harvest now, decrypt later
This is the part that should make every Sitecore architect sit up.
Imagine one of your users is on hotel Wi-Fi, filling in a form on an HTTPS site. Someone on the same network can run Wireshark and capture that traffic right now. They can't read it today, because TLS encryption is doing its job. But they can store it. And when quantum computers can break RSA and 2048-bit encryption, they'll come back and decrypt everything they hoarded.
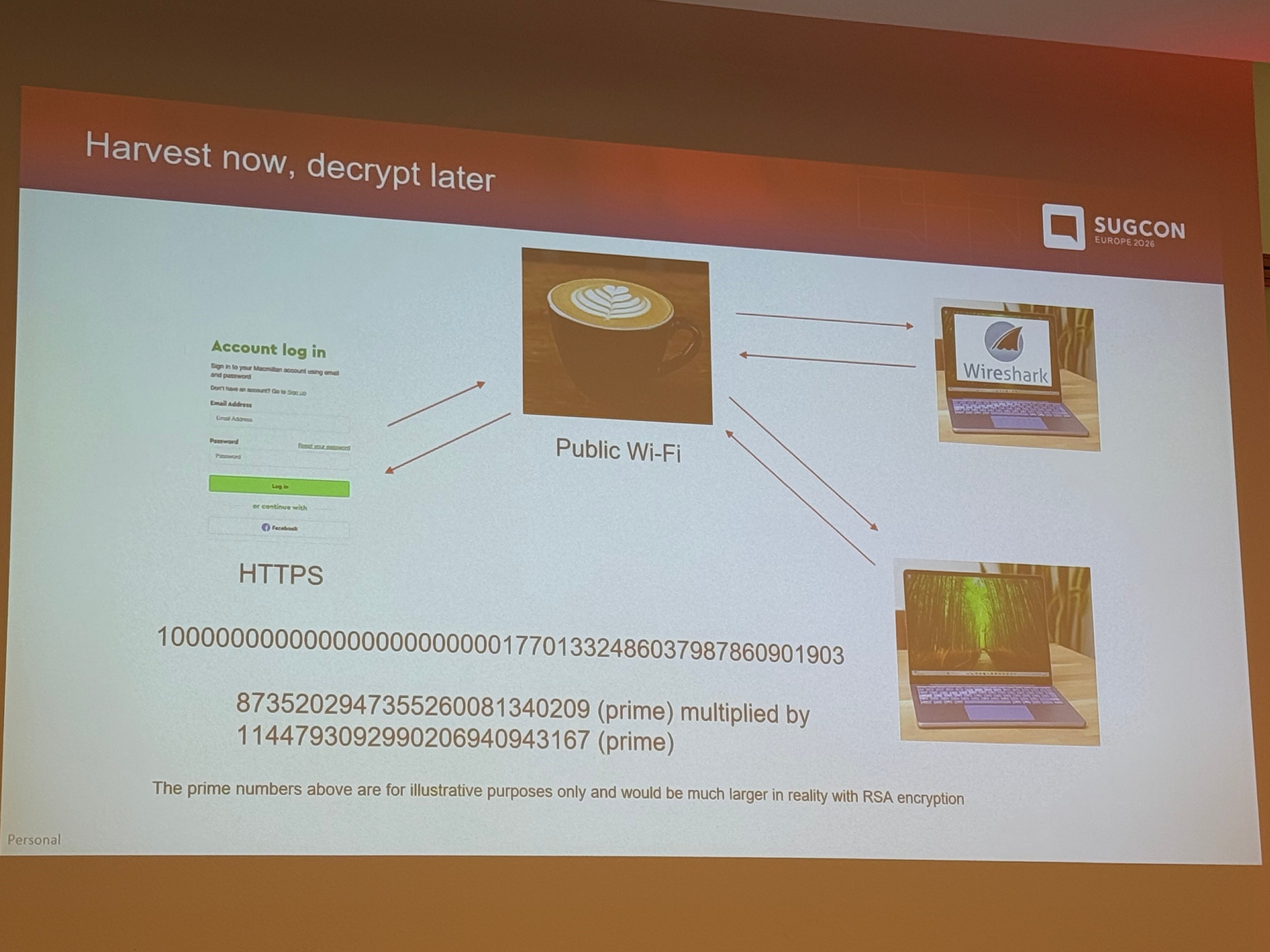
RSA relies on the difficulty of factoring very large composite numbers back into their two prime components. Easy to multiply two primes together. Very hard to work backwards. A capable quantum computer makes that hard problem easy.
So the threat isn't "someday our traffic will be at risk." The threat is that traffic flowing across your site today is already being harvested, and retrieval-augmented generation on top of large language models means insights can be pulled from huge stolen datasets more easily than ever.
If your data will still be sensitive in ten or fifteen years, and most sensitive data is, you already have a problem. Patient records don't expire. Financial history doesn't expire. Neither do trial participation, legal matters, or anything tied to an identity.
What Harald recommends you do now
Encrypt data at rest. Encrypt data in transit. Move to TLS 1.3 where you can.
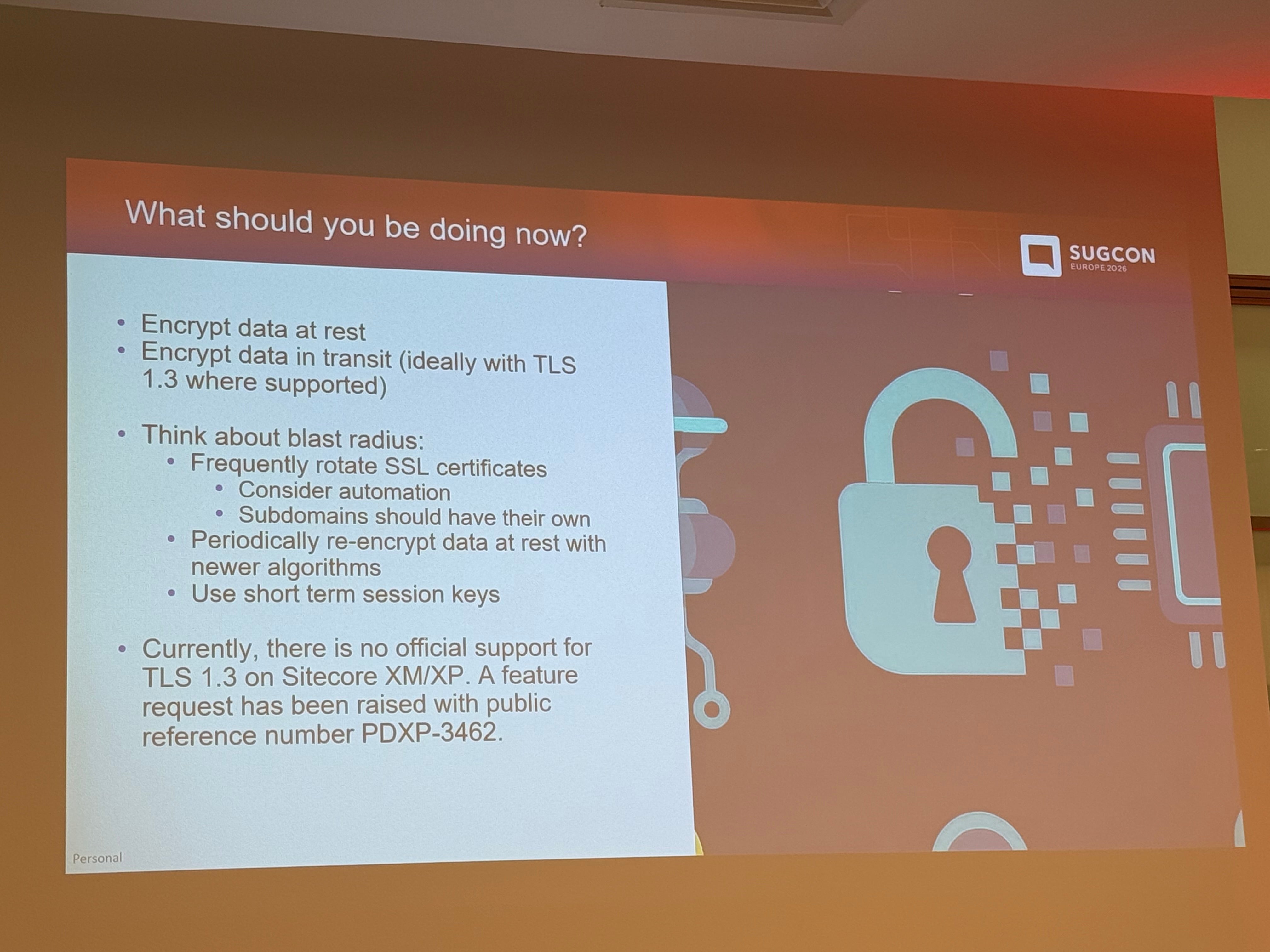
TLS 1.3 isn't quantum safe. But it gives you forward secrecy, which means traffic captured today can't be decrypted later using a key compromised in the future. That alone is a big deal. TLS 1.3 is also where the Internet Engineering Task Force is prioritizing post-quantum algorithm support, so it's the path forward.
Check your site's posture with SSL Labs. It's free and it tells you what ciphers your site is actually negotiating.
Limit your blast radius. Rotate certificates more often. The industry is moving this way whether you want it to or not. Public certificate lifetimes are down to 200 days, will be 100 days next year, and are headed to 47 days by 2029. Manual rotation at that cadence isn't a plan, it's a staffing problem.
Re-encrypt data at rest as your algorithms evolve. Use short-lived sessions.
The Sitecore piece for XM and XP customers
Here's where it gets specific. TLS 1.3 isn't officially supported in Sitecore XM and XP yet. A feature request is in. Until then, you have options.
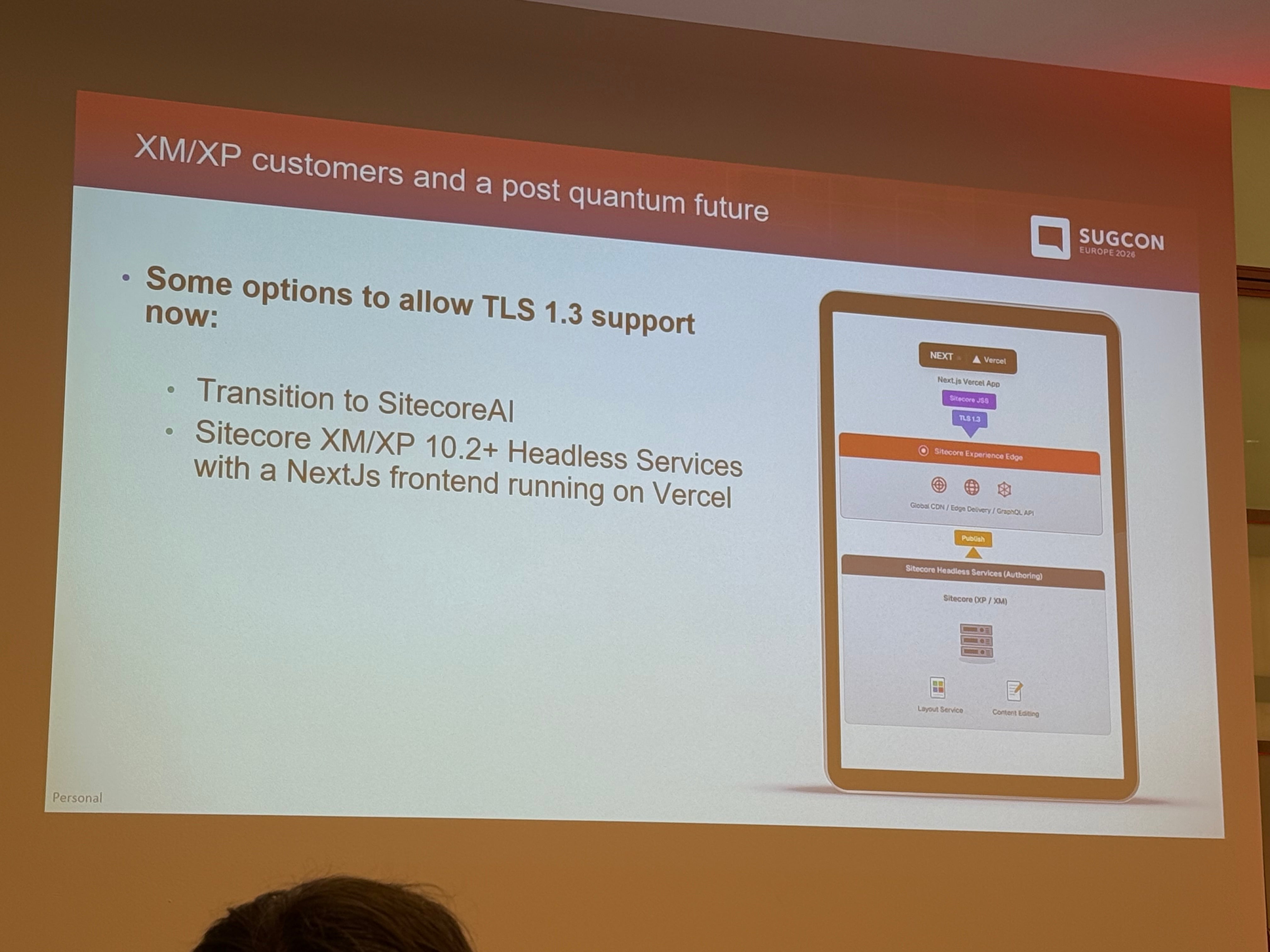
Option one: move to Sitecore AI (XM Cloud), where the edge framework terminates your connections over TLS 1.3.
Option two: stay on XM or XP 10.2 and run headless with a Next.js front end on Vercel. Your front end gets TLS 1.3. Your back-end connections between XP services (things like Experience Reporting) stay on TLS 1.2. You can push data back to XP through the Sitecore tracking service via Experience Edge, using the layout service and GraphQL endpoints you're already publishing.
Option two only makes sense if you're staying on XP for the foreseeable future. If you're moving to XM Cloud anyway, going headless-on-XP first means doing the JSS-to-Content-SDK work twice. Most teams should just pick the SXA pathway and get on with it.
The flip side
Quantum isn't only a threat. Harald pointed out that for Macmillan it opens the door to individualized cancer treatment predictions based on DNA sequencing that classical computers can't handle at scale. The same shift in compute that breaks today's encryption will unlock work that's currently impossible in drug discovery, materials science, logistics, fraud detection, and plenty of other fields.
Which is why you have to get the security posture right now, so you can still be in business when the upside arrives.
The post-quantum future
Post-quantum cryptography moves away from prime-based problems. The replacements are built on lattice-based problems in n-dimensional vector spaces. These are combinatorically explosive, with no known efficient polynomial-time algorithm, even for quantum computers.
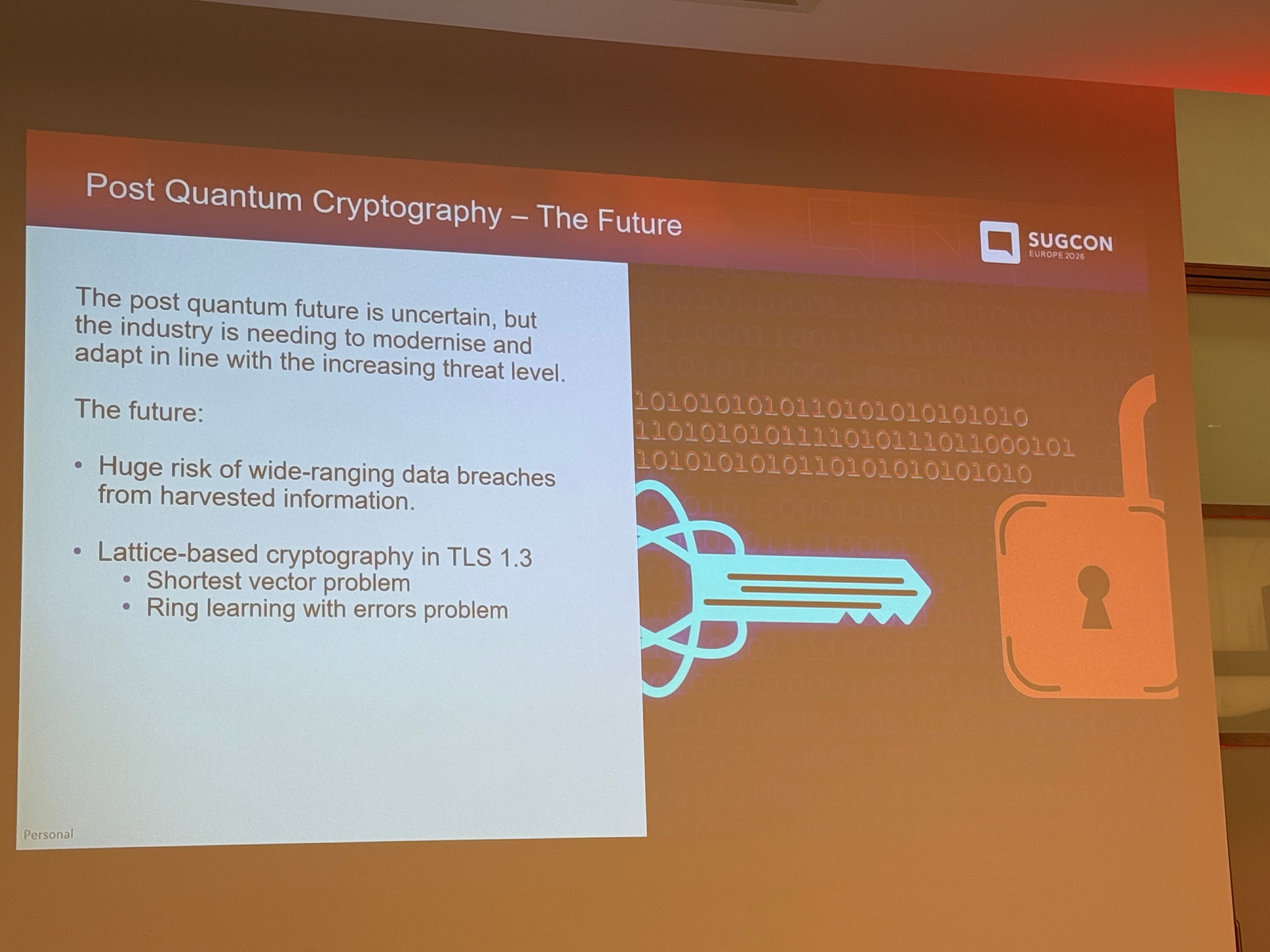
The migration will happen. TLS 1.3 is the on-ramp. Getting your estate ready is the work.
A thank you to Harald
Harald's session was one of the most practical, clearly-explained talks at SUGCON this year. He took a topic that most people glaze over at and tied it directly to the work Sitecore developers and architects are doing this quarter. If you missed it, his LinkedIn article covers the same ground and is worth your time.
At Konabos we help Sitecore customers think through exactly this kind of problem. If you want to talk through what TLS 1.3, certificate rotation, or an XM Cloud migration looks like for your specific setup, get in touch.

Akshay Sura
Akshay is a ten-time Sitecore MVP and a two-time Kontent.ai. In addition to his work as a solution architect, Akshay is also one of the founders of SUGCON North America 2015, SUGCON India 2018 & 2019, Unofficial Sitecore Training, and Sitecore Slack.
Akshay founded and continues to run the Sitecore Hackathon. As one of the founding partners of Konabos Consulting, Akshay will continue to work with clients, leading projects and mentoring their existing teams.


Share on social media